Pap Password Authentication Protocol Acronym Business Stock Vector (Royalty Free) 2018592065 | Shutterstock
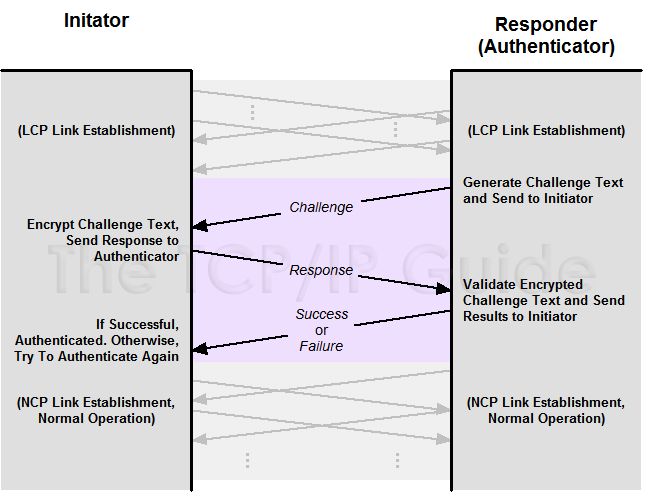
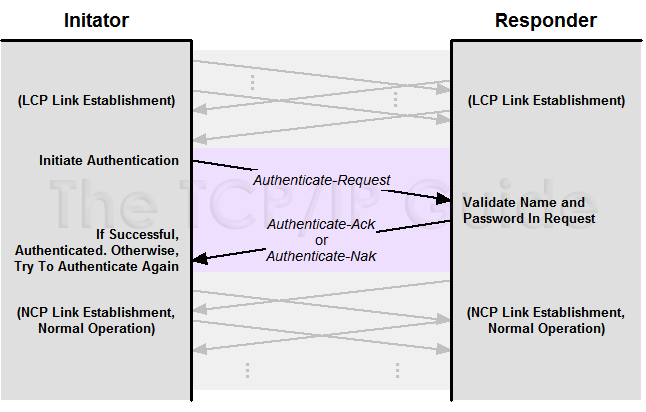
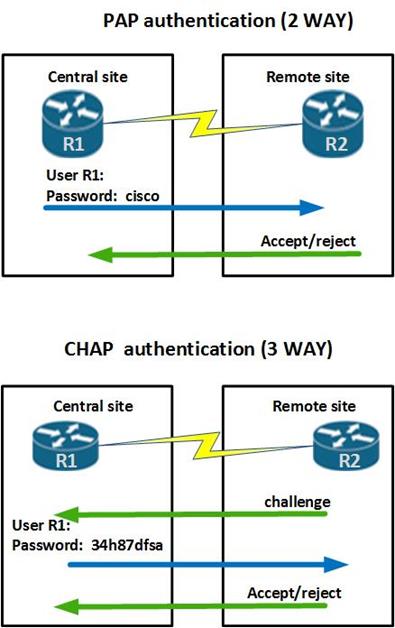
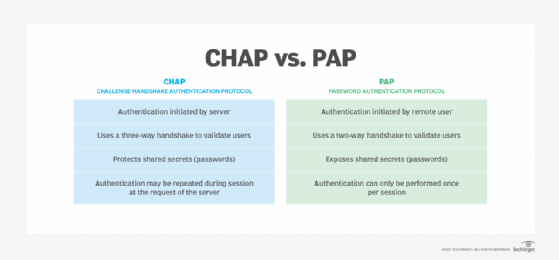
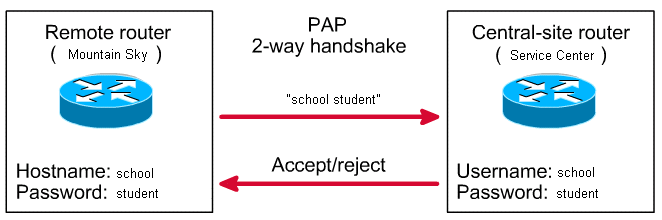
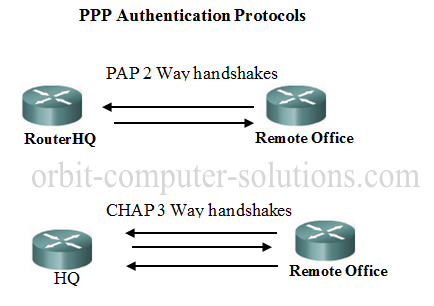
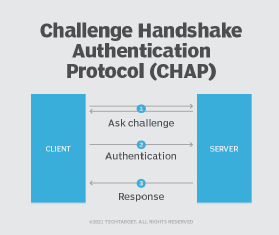
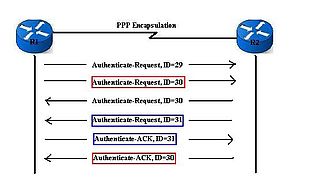
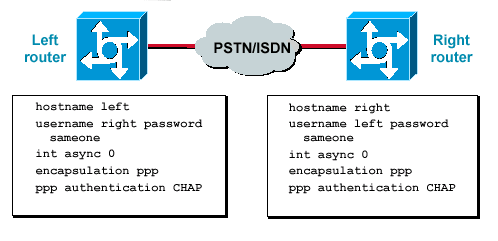
The TCP/IP Guide - PPP Authentication Protocols: Password Authentication Protocol (PAP) and Challenge Handshake Authentication Protocol (CHAP)

Pap Password Authentication Protocol Acronym Stock Illustration - Download Image Now - Acronym, Business, Computer - iStock
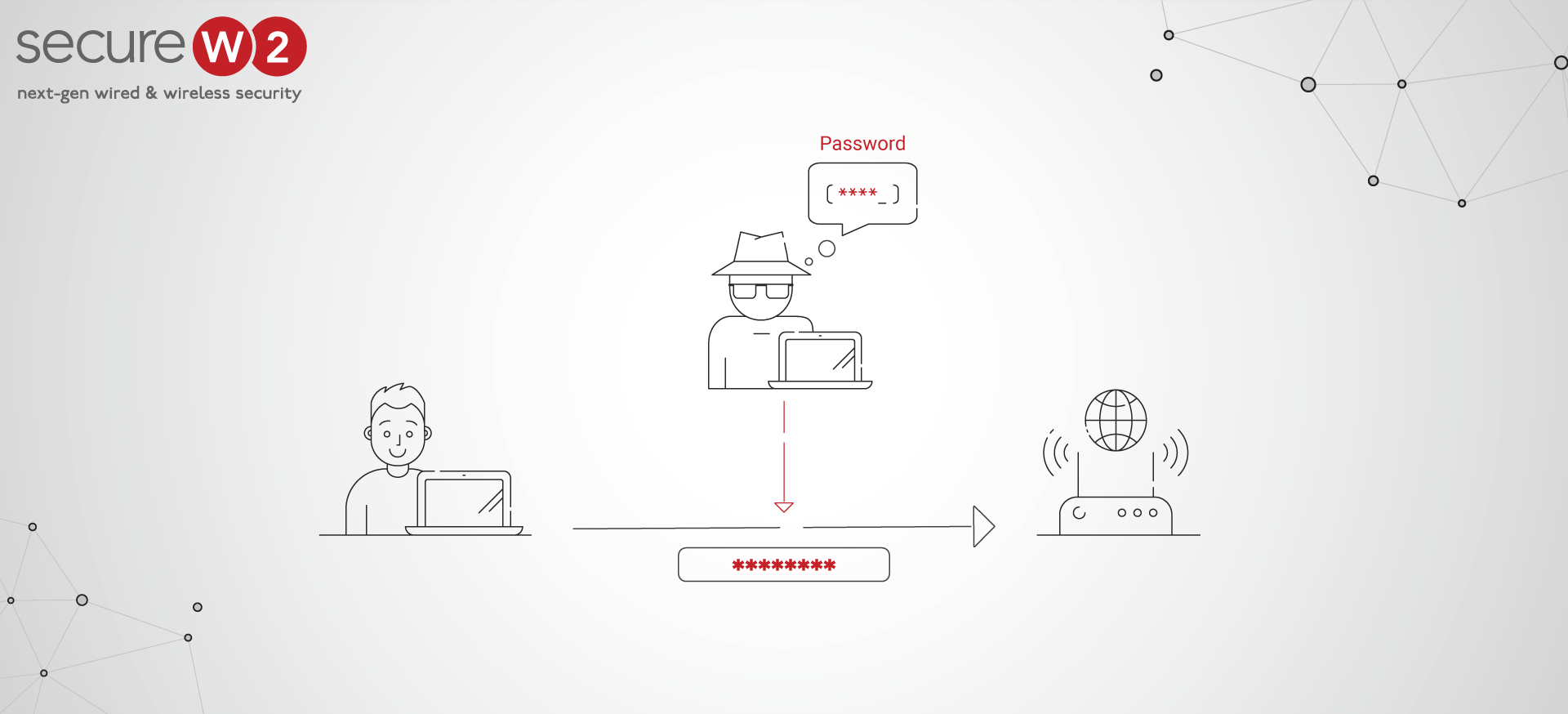
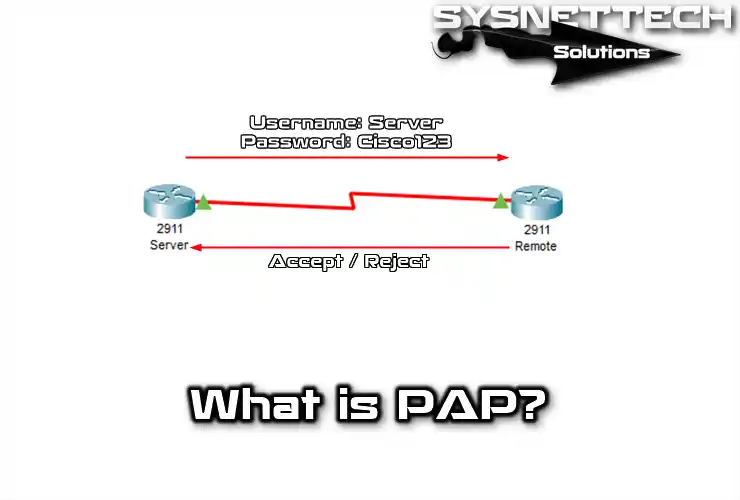
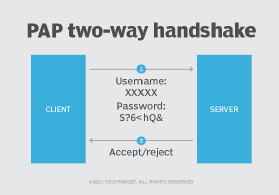
GitHub - Lithium876/PAP-POC: A proof of concept of how PAP (Password Authentication Protocol) works when authenticating users. This POC focuses on the fact that this protocol sends passwords our the network in